Focusing on the technologies again, the most commonly used instant messaging (IM) application was Microsoft’s Lync (24%), Skype for Business (17%) and regular Skype (17%), followed by Jabber (5%) and Microsoft’s OCS (4%). Facebook Messenger was used by only 3%. In the other categories notable mentions were Google Chat/Talk and Hangouts. However, most notable was the fact that more than a third of respondents (34%) did not use IM at all.
The survey asked if instant messaging would ever outstrip email as a faster and more effective means of communication. More than half (52%) disagreed, while a quarter did not know. Just less than one in four (23%) felt that IM could supplant email in the future. This, combined with the previous result showing a large section of organisations not utilising IM at all, perhaps reflects conservatism in the Irish market when it comes to business communication that retains a preference for formality.
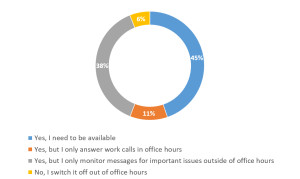
Security and content were also areas of interest for the survey. The majority (77%) indicated that the security of mobile devices was a concern for their organisation, with one in five indicating it was not. Just 4% were unsure.
Karl McDermott, head of ICT, Three Ireland, said that while the mobile network environment has brought huge benefits in terms of flexible working and productivity, it has also presented a heightened threat to security.
“It is understood that approximately 22% of the total number of mobile devices produced will be lost or stolen during their lifetime, and more than 50% of these will never be recovered,” said McDermott, citing research by Ernst and Young. “With employees now walking around with highly sensitive data in their pockets, it is not surprising that organisations are concerned about mobile security.
“However, it is often the case that this level of awareness does not exist amongst users. If someone leaves their laptop in a taxi, their first concern is the sensitive data that may be stored on the device. However, if they lose their phone or tablet, they often don’t have the same concern, even though their laptop is most likely encrypted and password protected and their phone is not.
“People using personal devices for corporate data presents a huge IT challenge and data protection is the biggest concern, especially where traditional consumer apps have infiltrated the corporate environment via the employees phone — Dropbox for example.
“Device manufacturers are also paying more attention to security concerns. Every new product and operating system that is launched is introducing more and more native security functions. iOS 9, for example, now has a minimum of a six digit passcode, instead of four.
McDermott advises that the three basics steps for mobile security should be to ensure that all mobile devices are password protected; secondly, to encrypt them; and thirdly, to ensure they can be accessed remotely to allow them to be wiped if lost or stolen.
“There is no doubt that the risk involved is a concern,” said McDermott, “even just the financial cost to companies of a data breech is staggering. This can be alleviated for as little as €3.50 a month for a mobile device management licence.”
Respondents were asked if their IT department had the capacity to deal with mobile support and security. Two thirds (66%) felt that they did, while more than one in five (22%) felt they did not, with balance saying they did not know. This represents a worryingly large proportion of Irish organisations that are less than sure about their ability to deal with mobile security and support.
McDermott observed that while IT departments are very good at looking after PCs and laptops, they tend to be less familiar with protecting mobile devices.







Subscribers 0
Fans 0
Followers 0
Followers