“The bad news is that pretty much half are blind to layer 7 attacks and have no Layer 7 protection, unless their applications have no vulnerabilities at all as the code is properly hardened and bug scrubbed, but generally this isn’t the case with applications,” said Liverpool.
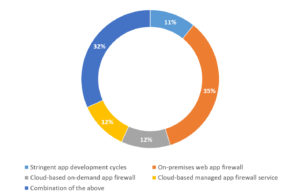
The survey asked about organisations’ approach to securing web applications. More than a third (35%) said they employed an on-premises WAF, with cloud-based on demand application firewalls and managed application firewall services coming in at 12% each, while almost a third (32%) said they use a combination of all of these measures. Some 11% said they use stringent application development cycles as their means to secure web applications.
“The positive here,” Liverpool observed, “is that any application security is a good thing and there are several ways this can be achieved. All options require human input, which always means there is a chance of errors being made and a vulnerability not being protected. What this means is that on top of the tools there needs to be a policy and procedure wrapped around this to double check and validate the human component to try and remove any errors that may have been inadvertently made.”
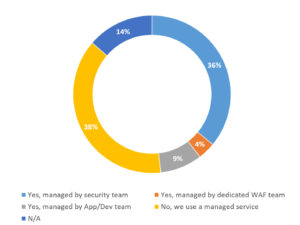
Skills are once again an issue in managing security measures, and WAFs are no different. More than a third (36%) said that they had the skills to manage their WAF and did so through an in-house security team, while slightly more (38%) said they had the skills through the use of a managed service. For 14%, the question was not applicable, while almost one in 10 (9%) said the WAF was managed by an application or development team. Just 4% have a dedicated WAF management team.
“The people we have found to have the right skills to manage a WAF are the App/Dev teams or a dedicated WAF team,” reported Liverpool. “In this survey, only around 12% are using these methods. Security teams and managed service providers generally are not proficient with WAF’s or aren’t close enough to the applications to properly understand how they can very tightly secure the applications.”
The survey results show a developing story in relation to DDoS, general threats to web applications and what to do about them. While awareness of DDoS efforts is certainly widespread, thankfully, the incidence of such efforts for Irish organisations seems small — for now.
While there is also a broad spread of mitigation techniques, Liverpool’s observations as to the suitability of some of those measures shows the level of awareness and knowledge as what is best leaves something to be desired. Furthermore, even where appropriate measures are in place, the management of same seems somewhat fragmented, as evidenced by just 13% having either a dedicated or application/development team management.
Irish organisations have an opportunity here, with a relatively low level of incidents as yet, to seize the initiative and implement appropriate mitigation solutions, with properly managed policies and teams. Before the menace grows to become a ubiquitous threat, there is time to get a head of the black hats. While there is never such a thing as invulnerability, there is certainly the opportunity to be the least attractive, or susceptible, target. As has been observed by many information security professionals, it is only when a revenue stream for a cybercrime is reduced or cut off that it fades away. With a concerted effort, Irish organisations can ensure that this island yields a poor return for such crimes, perhaps hastening their end altogether.







Subscribers 0
Fans 0
Followers 0
Followers