The survey then asked specifically about DDoS incidents. Just 14% said they had been targeted by DDoS, with almost the same proportion (16%) saying they did not know. Almost a quarter (22%) said they were certain they had not been subjected to a DDoS attack, while more than a third (37%) said they were fairly certain they had not been targeted.
“The stats here are once again highlighting that visibility and having the right tools is key,” said Liverpool. “Many of the respondents not being able to 100% confirm or deny whether they had suffered with a DDoS attack is worrying. We know that DDoS can be used as a masking tool to hide many more sophisticated attacks aimed at getting information, valuables or causing damage to systems.”
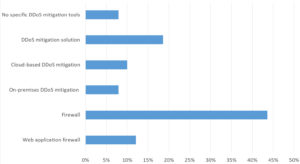
Respondents were then asked about mitigation and protection measures for such attacks. Almost half (44%) indicated a their primary solution was firewall, followed a long way behind by a hybrid cloud and on-premises DDoS mitigation solution (19%), with web application firewalls (WAF) coming in at 12%. Cloud-hosted mitigation solutions were at 10%, some 2 percentage points ahead of on-premises solutions. Most worryingly 8% said they had no specific tools to mitigate such attacks.
Liverpool warns that network firewalls have some significant shortcomings in protecting against DDoS attacks.
“The first thing that normally brings down a service is the internet bandwidth being exhausted, and this happens in the internet pipe before the CPE router and firewall. Application level DDoS happens at a technology level that a standard firewall cannot see. Typical network firewalls perform badly at decrypting SSL traffic and so generally just allow it through which could be allowing through an application level DDoS. Firewalls haven’t been designed for the size of today’s volumetric DDoS and so could be the weak link in their security chain.”
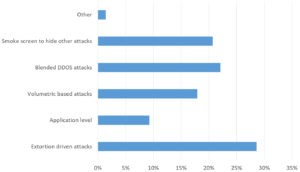
Respondents were asked what they perceived as the biggest threat from DDoS actions. In the lead was extortion-driven attacks at nearly a third (29%), followed by blended DDoS attacks (22%) and diversionary tactics to hide other attacks (21%). Interestingly, application-aimed attacks only came in at 8%. This tallies with the recent experiences of many sufferers, where extortion demands were made in advance of a DDoS attack.
When asked whether organisations had deployed a web application firewall, half said yes, with 40% saying no, and 11% who did not know. This contrasts with the earlier question on specific DDoS mitigation measures, where just 12% indicated that a web application firewall was their principle mitigation solution.
“Half the organisations here have a WAF,” said Liverpool, “which is good for them if they are implemented and managed properly to at least mitigate the OWASP top 10 attacks. However, in my experience those who have implemented WAF’s in that way is low. Many organisations find running a WAF properly in blocking to be complicated or too time consuming. The other half of organisations have no WAF at all so would be open to layer 7 attacks as well as completely blind if they were under attack so that is even worse.”
Respondents were asked about the criticality of WAFs to their security infrastructure and more than half (53%) agreed, but a further 17%, while agreeing, are only planning to deploy one. Almost a third (31%) said they rely on other mitigation measures.
Liverpool was appreciative of the majority who recognised the importance of WAFs in security infrastructure, but was wary of the dangers for the rest.






Subscribers 0
Fans 0
Followers 0
Followers