A term that has entered the non-technical lexicon recently is distributed denial of service (DDoS) attack. To date, domain name service providers, banks, government agencies, and most recently a major European telecoms provider, have all been the subject of these often crippling, or indeed, disabling attacks, ensuring the term a broader exposure than just among the information security community.
TechBeat, in association with F5 Networks, gauged the Irish situation asking about perceptions, experiences and mitigation of these and other cyberthreats, polling 141 Irish IT professionals. The answers, while not necessarily surprising, show that far from a distant problem, the threat of DDoS attacks is all too real on this island.
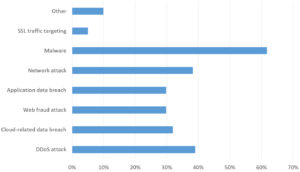
The survey began by asking about current perceptions of security concerns, with respondents prompted for their top three. The lead by some margin, at nearly two thirds (62%), was malware, followed by DDoS attack (39%) and network attacks (38%). Following reasonably closely (32%) was cloud-related data breaches, perhaps indicating that cloud acceptance is growing as trust improves and security measures develop. In the ‘other’ category, though only 10%, the common response was a specific type of malware, ransomware.
“The survey shows,” said Tristan Liverpool, director of Systems Engineering, F5 Networks, “that the biggest concerns are around the applications, data and service availability. These attacks are at a higher level in the Open Systems Interconnection (OSI) stack than the traditional network attacks of the past and new more app centric approaches are needed to combat them.”
With the awareness of threats as it is, the survey asked if organisations had a cyber-incident response plan in place. Almost half (43%) indicated they did, while more than a fifth (21%) said there was no such plan in place. Nearly a third (29%) said their organisation was developing a plan, but a worrying 6%, though small, said there were no plans to develop a cyber-incident response plan.
“Over 56% companies don’t have a cyber security plan in place, which is a very worrying statistic,” said Liverpool. “This is a very risky situation for any organisation to be in as all organisations have on-line connectivity, which means any of them could be a target at any time. If the protection mechanisms in place are penetrated every organisation needs to know what their action plan is to keep the crown jewels safe, as well as to know how to mop up any damage and destruction caused.”
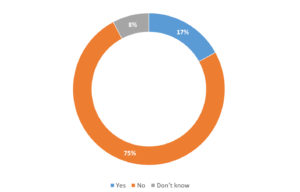
To establish the extent of cyber-incidents among Irish organisations, the survey asked is organisations had suffered a significant cyber-incident in the last 12 months. Some 17% said they had, compared with three quarters who said no. Just 8% did not know.
“The interesting thing here is only 17% know — or admit — they have suffered a cyber-incident in the last 12 months,” said Liverpool. “The reason this is interesting is that, over the last few years, we have seen organisations such as LinkedIn and Dropbox reveal they have been hacked years after the incident happened, as they have discovered evidence of the breach from external entities, and then have realised and investigated. What this highlights is that visibility, the right tools and knowledge of the infrastructure is key to at least know if cyber-incidents are occurring even if they weren’t stopped by the tools and policies in place.”





Subscribers 0
Fans 0
Followers 0
Followers