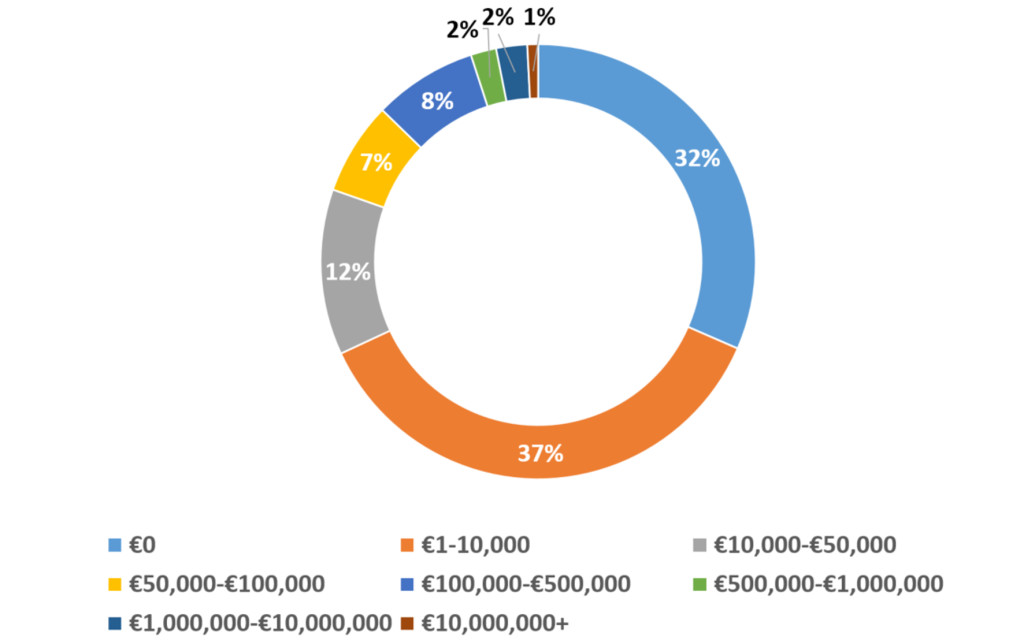
In the last 12 months, what was the total financial cost of cybercrime/security breaches to your organisation in terms of protection, response and damage?
“We always suggest to clients,” added Larkin, “that they complete an organisational risk assessment, which will highlight the risks, their impact and likelihood of occurring. This provides a very practicable and prioritised ‘to do’ list. Without this, mitigating the latest trend based on whatever a vendor is promoting can lead to spend being placed in the wrong area for your business.”
With any data breach or cybersecurity incident, there is always the threat of litigation. While the vast majority said that their organisation had not been involved in such litigation in the last three years, 5% said that they had, with 18% saying that they did not know.
“There are still a relatively small number (5%) of organisations which have been the subject of litigation proceedings as a result of security incidents,” commented Larkin, “but we anticipate this will grow over time, particularly as the costs and impacts of these incidents rise.”
Over the same time period, respondents were asked if their organisation has had to retrieve documents or data in relation to legal proceedings. More than a third (35%) said they had not and 22% did not know, but 43% confirmed that they had done so.
“Our experience,” said Larkin, “echoes the needs of 43% of organisations which recognise the growing need for information technology and security to improve the efficiency of data discovery as part of the legal process. The burden of discovery is now a key part of some legal teams’ strategy. In some cases it is used to try and distract attention and process from more substantive issues and it is becoming increasingly important that organisations have strong information governance and supporting information management technology in order to stay the pace on litigation and the discovery process. The focus on reducing the significant costs and burden of litigation support is important, as is improving responsiveness and accuracy via appropriate eDiscovery and forensics systems.”
The survey asked about the three most significant security threats to the organisation. The number one threat by a small margin was reputational and brand harm (74%), followed closely by loss of confidential or proprietary data (70%). Some way behind these in third was critical operation disruption (55%). Loss of customers and loss of revenue were tied in fourth (33%).
“The findings are further confirmation,” said Larkin, “that the long-standing top three business risk drivers for information security remain: avoiding loss of data; prevention of harm to reputation and brand; and the availability of critical services.”
With such widespread recognition of the potential threats to business in information security and cybercrime, it was somewhat surprising that more than half of respondents said their organisation either did not (26%) prioritise security spending based on risk, or did not know (25%) if that was the case.
“What is notable and encouraging,” observed Larkin, “is that organisations are starting to focus their information security spend on a prioritised risk basis rather than a scattergun approach. No one has an infinite security budget so we continuously highlight the importance of a fully informed, prioritised and risk-based approach to our clients. This maximises the potential return on their information security spend.”








Subscribers 0
Fans 0
Followers 0
Followers