Almost one in four (39%) organisations said they audit their data for compliance with data handling policies at least once per year, with a fifth saying they do it at least once per quarter. Some 14% audit less frequently than annually, but a combined 27% either do not have a policy for data handling or do not audit data for compliance at all.
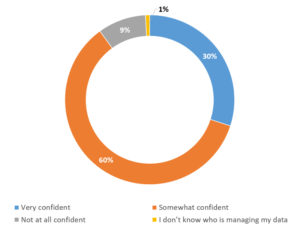
How confident are you that staff are trustworthy and knowledgeable enough to handle your data?
“Whilst it is positive to see that the majority of organisations have data handling policies and perform regular audits, in this day and age it is worrying that a significant amount of organisations do not have data handling policies nor do they audit for compliance with polices,” said Larkin. “These organisations are effectively ‘hitting in hope’ rather than managing and controlling their destiny in terms of information security risk management and compliance.”
The survey asked if organisations had policies, procedures and controls for third party access to their data, such as suppliers, outsourcers and data processors, and whether security compliance audits were carried out in these cases. Worryingly, nearly a quarter (22%) had no such policies, with more (29%) saying that such policies existed but that third parties were not audited. A combined 43% confirmed that there were such policies and audits, and the proportions broke down into 14% that only audited at the start of an agreement, 6% that audited quarterly, 12% that audited annually and 11% that audited less frequently. Just 6% did not know if such policies were in place.
Larkin commented that the reults were particularly worrying when considering the continuous, high profile incidents of data breach and data loss partly or wholly caused by third parties to organisations, both at home and internationally.
“Third party access to an organisation’s data typically presents a higher risk than own staff access,” said Larkin. “From our experience of auditing this area, a significant number of third party organisations talk the talk with respect to policies and controls, but don’t always ‘walk the walk’ on a day to day basis. So, verification of the application of processes and controls is equally important in terms of trying to manage this third party risk.”
“We are also seeing the emergence, particularly in the last 12 months, at enterprise B2B level, of onerous supply chain due diligence and contracting. This suggests that those organisations who don’t have policies or don’t conduct audits of third party access will need to change rapidly if they plan on doing or continuing to do business with these enterprise business customers.”
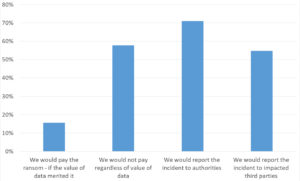
If a data breach led to your organisation being held to ransom in the past or in the future…
“Our view,” Larkin warned, “is that within the next 24 months most organisations planning on doing business with enterprise B2B will need ISO 27001 accreditation in order to be selected or re-validated as a supplier to these enterprise customers. Clarity on accreditation for Government or public sector may emerge in light of the new appointments at GCIO level.”
With ransom attacks now a common occurrence, respondents were asked about the extent of such demands within the last 12 months. Thankfully, for the majority (67%), this was not applicable, but 13% had seen demands up to €500. Some 8% saw demands from €500 to €999, while 6% saw the €1,000 to €4,999 range, and just 3% the €5,000 to €20,000 range. There were also single instances reported of demands for between €100,000 and €999,000, and one for more than €1 million.
With regard to these demands, the survey asked about responses in the future. With respondents selecting all options that applied, the most popular was informing the appropriate authorities (71%), followed by a complete refusal to pay (58%). More than half (55%) would inform any third parties impacted, and just 16% would pay the ransom if the affected data merited it.
The results were broadly in line with what was being seen in the wider market, said Larkin.
“16% of organisations have acknowledged the reality that if the right data was encrypted, and there was no other viable means of releasing this data, then they may pay the ransom.”
“Also, whilst the significant majority 71% of organisation would report this to authorities, a still significant 29% would not, perhaps pointing to traditional under-reporting in this area for Ireland. We would presume that as ransomware evolves from leaving data in situ and encrypting it to exfiltration and threatened public disclosure unless a ransom is paid, that the reporting levels would increase, driven by compliance obligations with respect to loss and disclosure.
“However, international norms do point to up to 60% of data loss or data breach incidents not being reported to authorities and impacted third parties by the organisations suffering these breaches.”







Subscribers 0
Fans 0
Followers 0
Followers