Keating felt that despite these perceptions, the rise of both mobile and social media would likely present problems in the future.
“The Third Platform brings with it increased and new cybersecurity risks,” said Keating. “Historically, Irish businesses have used IT applications and systems that were introduced by the business itself, such as finance packages or Office 365. Now, with the advent of IT consumerisation, users are bringing systems like Gmail, Dropbox or Evernote into the business, sometimes without the knowledge of the business.”
Keating warned that a user might email a document or data to private email account so they can work on it in the evening, but while good for productivity, this is potentially putting very sensitive information at risk.
“If the IT department is aware of the practice, they can deploy tools that can be used to access data the worker needs, but to do so in a secure way,” said Keating.
Despite media coverage of high profile cases of apparent nation-state cyberespionage, a large proportion did not think that this was a likely threat (45%), but more than a third (37%) thought it may be a threat with a further 10% thinking it will become so.
“I’m surprised that nation state cyberwarfare attacks are not a more pressing concern for more of the respondents,” said Keating. “Every internet-connected business around the globe is a potential target, or a stepping stone to a target.”
“Given that Ireland is home to some of the largest technological organisations in the world, both the country, and businesses within the country that have links to these organisations, are extremely likely targets. Our digital links to the best known global tech brands make us a real target for cyberattacks and this is something that needs to feature prominently on the agenda.”
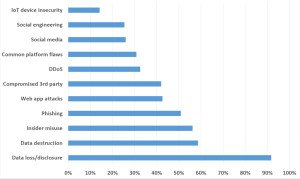
What is clear from the survey is that there are varying perceptions of responsibility for information security, though overall awareness seems to be good. Perceptions as to the likely sources and causes of breaches or losses show that IT professionals are largely focusing their efforts in the right place, though perhaps could prioritise a bit better based on actual metrics, such as breach reports and analyst reviews.
The lack of awareness around third parties such as suppliers is also worrying, as many major breaches in recent years have been shown to have started with contractors, suppliers or other part of the supply chain, and Irish organisations need to more aware of the fact that they could be an attack vector for an organisation they work with, as much as being a target themselves.
It is reassuring to see that there is high awareness of the insider threat — employees themselves, whether malicious or not. Again, breach reports and investigations have consistently shown that this particular source to be very common. However, this is contrasted with the fact that staff are likely to be the source of a breach due to social engineering, but that risk ranked only 11 out of 12, on below social media as a cause of a breach. This may betray a lack of awareness of the power of both of these methods to extract intelligence that may lead to a successful compromise effort.
The survey results reveal a largely positive outlook for information security risk management with a few areas of concern. Constant review of measures and increased communication and education should go some way to tackling those problem areas.






Subscribers 0
Fans 0
Followers 0
Followers